How to Configure Apache Web Server in Redhat Linux
This tutorial explains how to configure Apache Web Server in Linux step by step with practical examples. Learn how to configure virtual hosts, configure user’s home directory as web root, change document root, deploy a basic CGI application and allow HTTP & HTTPS traffic through Linux firewall and SELinux.
Apache is the most popular, secure, robust, reliable and powerful web server. Apache is used by more websites than all other web servers combined.
In this tutorial I will use three systems Server, linuxclient and windowclient from our LAB environment. I will configure Apache Web Server on Server system and test from inuxclient and windowclient system. If you want to check the network topology used in this article please check following article. Lab set up for RHEL practice
Installation of Apache
Two packages are required for Apache server
- httpd
- mod_ssl
- elinks
httpd package install Apache web server.
mod_ssl is the additional package which required to create secure websites
elinks is the additional package for text based web browser.
If you have yum repository configured use following command to install Apache web server with additional package
# yum install –y httpd mod_ssl
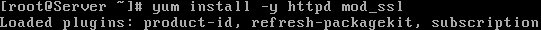
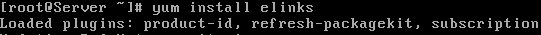
# yum install elinks
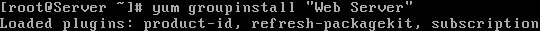
Or you can do it in more simpler way by using groupinsatall. With following command you can install mandatory and all default packages.
# yum groupinstall "Web Server"
If yum repository is not configured use rpm command to install necessary RPM. Mount installation disk of RHEL6 in media folder and move in Packages folder.
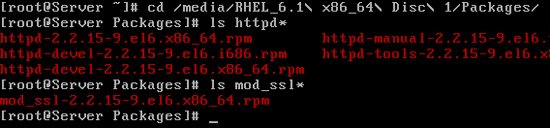
Run following command to install httpd
#rpm -ivh httpd* --nodeps --force

Run following command to install mod_ssl
#rpm -ivh mod_ssl* --nodeps --force

Run following command to install elinks
#rpm -ivh elinks* --nodeps --force
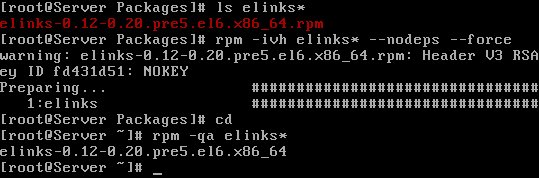
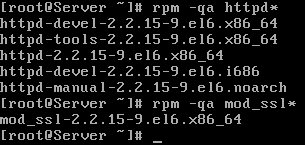
Verify that the packages were installed correctly
Run following command to start service when the system boots

Start httpd service

httpd service requires at least one active network connection, if it does not detect any active connection it will throw following message
Starting httpd: httpd: apr_sockaddr_info_get() failed for Server
httpd service try to resolve system IP with domain name. It will throw following error, If it fails to resolve.
httpd: Could not reliably determine the server's fully qualified domain name, using 127.0.0.1 for ServerName
In real world DNS Server are used to bind IP address with domain name. In LAB environment where we have limited systems , we can also use hosts file for this purpose.
Open /etc/sysconfig/network
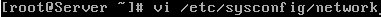
Change hostname to Server.example.com and save the file
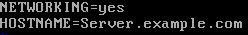
Reboot the system

Verify that hostname is changed

Before we update hosts file on server also verify the hostname and ip address of linuxclient

Now on server open /etc/hosts file
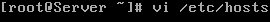
Add entry for server and linuxclient system and save the file

Verify the network card status

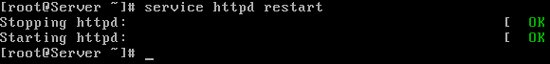
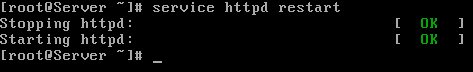
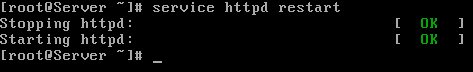
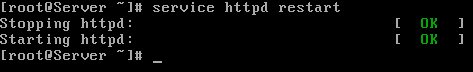
Now restart the httpd service
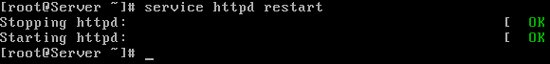
Default versions of httpd create a generic web server service which is sufficient for most basic operations. Once httpd service is running start web browser and enter a URL http://localhost

Same testing can be done form text based web browser ,If GUI is unavailable.
# elinks 127.0.0.1

We got Apache test page which confirm successful Apache configuration.

Exit from the ELinks browser. Press Q, and when the Exit ELinks text menu appears, press Y to exit Elinks.
We have successfully installed Apache Web Server. So far its a generic web server service, to make it a regular and a secure web server, we need to configure it.
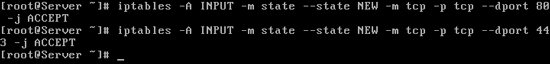
IPTABLES Firewall rules for web Server
Default installation of Apache web server use port 80 for HTTP traffic and 443 for HTTPS traffic.
You can create custom iptables rule to limit access to one or more networks or systems. For example following rules allows access to every computers on 192.168.1.0 network except one with IP address 192.168.1.25 over port 80.
-A INPUT -m state --state NEW -m tcp -p tcp -s 192.168.1.25 --dport 80 -j REJECT -A INPUT -m state --state NEW -m tcp -p tcp -s 192.168.1.0/24 --dport 80 -j ACCEPT
We have a well written article for IPTABLES firewall, use that to create custom firewall rules for web server. For this article create rules to allow all traffic on port 80 and 443.
#iptables -A INPUT -m state --state NEW -m tcp -p tcp --dport 80 -j ACCEPT #iptables -A INPUT -m state --state NEW -m tcp -p tcp --dport 443 -j ACCEPT
Save the firewall rules you have just created and restart the iptables service
# service iptables save # service iptables restart

Until you change the value of DocumentRoot directive in httpd.conf file , Apache looks for web pages in default location /var/www/html directory.
To get your web server up and running, all you need to do is to transfer the web pages or websites in /var/www/html directory.
We will make two websites for testing. We will use most simple html web page for testing.
Make two directories mysite1 and mysite2 in /var/www/html folder
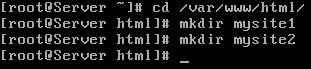
Make a sample html page in both directories

Our sample websites are ready for use.
Configure SELinux for web server
Use following command to check all associated SELinux Booleans with httpd
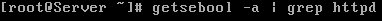
Most of these options are self explained and relate to interactions with other services. for example httpd_enable_ftp_server allow Apache to act as an FTP server, which is out of scope for this article.

Default enabled SELinux options
| Booleans | Descriptions |
| httpd_builtin_scripting | Used to provide permission for php content |
| httpd_dbus_avahi | Supports access from HTTP services |
| httpd_enable_cgi | Allows HTTP services to execute GCI scripts |
| httpd_tty_comm | Enables communication with controlling terminals |
| httpd_unified | Supports read/write/execute access by httpd_t files |
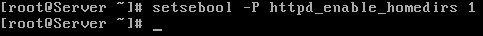
httpd_enable_homedirs supports access to files from user home directories, default value is off. We will enable it later in this article.
Default enabled options are sufficient to provide basic web services , you do not need to make any changes. But you need to configure SELinux contexts, user context is system_u and the type is http_sys_content_t.
Check the current context of the files
#ls -Z /var/www #ls -Z /var/www/html

We need to set context of any newly created file or directory for the web server user to be able to access it.
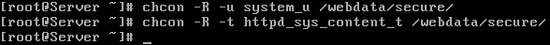
Use the chcon command to change the context
#chcon -R -u system_u /var/www/html #chcon -R -t httpd_sys_content_t /var/www/html/
Verify that all the context fields have been changed correctly
#ls -Z /var/www/html

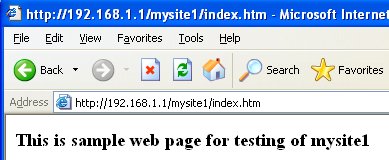
Test these websites form linuxclient system [make sure client system have elinks rpm installed]
elinks 192.168.1.1/mystie1/index.htm
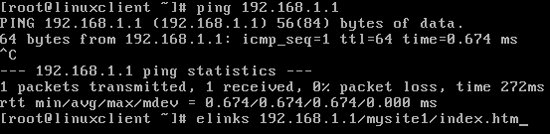
Verify the site

Close elinks

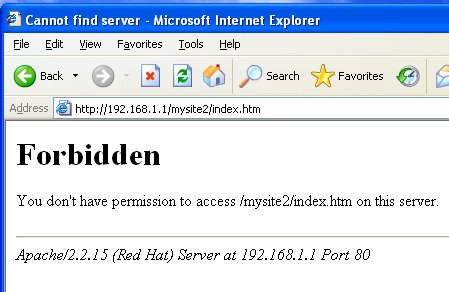
On window client open browser and type 192.168.1.1/mysite2/index.htm
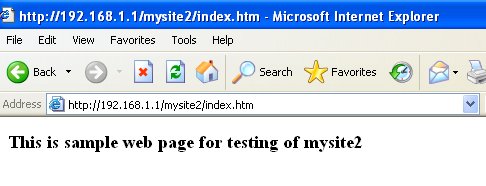
We have set up Apache web server with default configuration.
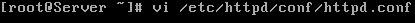
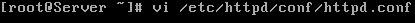
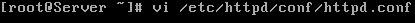
Back up the default httpd.conf file on a safe location.
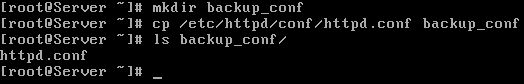
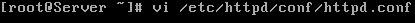
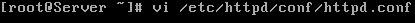
Open the /etc/httpd/conf/httpd.conf
This is the main configuration file for httpd web service and completely usable right out of the box for generic web service.
This file is grouped in three sections and each section is well commented
- Global environment directives that control the whole operation of Apache server process.
- Directives that define the parameters of the main or default server, which responds to requests that are not handled by a virtual host. These directives also provide default values for the settings of all virtual hosts.
- Settings for virtual hosts, which allow Web requests to be sent to different IP addresses or hostnames and have them handled by the same Apache server process.
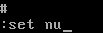
To make navigation easier, turn on line number ESC Key + : +set nu + Enter Key
Host-Based Security
If server have multiple IP address, you can limit the IP address and port on which the server can listen for incoming connection. By default server listen on port 80, but can be update as well.

For example to limit server only to listen on IP address 192.168.1.1 with port 80 Set Listen Directive
Listen 192.168.1.1:80

Now Server will listen only on the 192.168.1.1 IP address on port 80 for incoming requests.
Apache also let you configure the hosts which should be allow to access to web server. <Directory> section allow you to specify the hosts base security.
| Value | Example | Descriptions |
| Allow from all | Default value, allow access from all hosts | |
| Allow from [IP Address] | Allow from 192.168.1.10 | To allow only a specific IP or host |
| Allow from [Host name] | Allow from linuxclient | To allow only specific host |
| Allow from [Network] | Allow from .example.com | To allow only example.com network |
| Allow from [Network] | 192.168.1.0/24 192.168.1.0/255.255.255.0 |
To allow only from 192.168.1.0 network |
| Deny from all | Deny access from all hosts | |
| Deny from [IP Address] | Deny from 192.168.1.10 | To Deny only a specific IP or host |
| Deny from [Host name] | Deny from linuxclient | To deny only specific host |
| Deny from [Network] | Deny from .example.com | To deny only example.com network |
| Deny from [Network] | 192.168.1.0/24 192.168.1.0/255.255.255.0 |
To deny only from 192.168.1.0 network |
For exam remember
- If DNS service is unreliable use IP address.
- When specify domain name to allow or deny from, make sure you include the leading dot[.]
- When specify a subnet, there is no ending dot[.] at last octet.
- Order play the most important role, when set allow or deny access.
- If you set Order allow, deny Only those host names or IP addresses associated with allow directive are allowed access. All remaining hosts or IP address would be denied.
- If you set Order deny, allow Only those host names or IP addresses associated with deny directive are denied access. All remaining hosts or IP address would be allowed.
Default value is Allow from all
In our LAB setup we have two clients linuxclient [192.168.1.10], and windowclient [192.168.1.20]. Lets allow access only to linuxclient system.

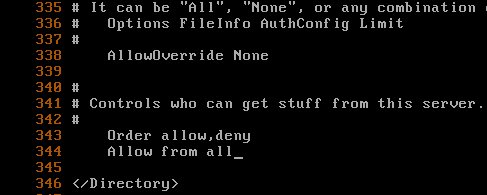
Save the file and restart the httpd service
Try to access same websites again from both client systems. This time linuxclient system would be able to access web server as usual, but on windowsystem you will be denied
User-Based Security
User based authentication provides a way to allow only certain users or group to access web server.
We can use following options to configure user based authentication.
| Options | Descriptions |
| AuthType | Defines the authentication method |
| AuthName | Comment for the users |
| AuthUserFile | File used to define username and password |
| AuthGroupFile | File used to define groups |
| Require | Specifies the users or groups that can log in |
Open httpd.conf file again
In last practice we have restricted all hosts except one

Before we do this exercise lets allow all hosts to access the web server.
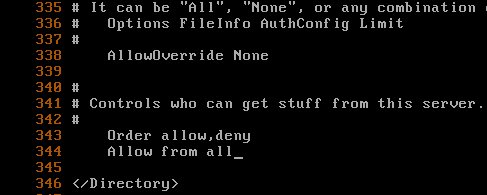
In < directory > section add following and save the file
AuthType Basic AuthName “Password Restricted Area” AuthUserFile /etc/httpd/userauthfile Require user rhceuser01

Use htpasswd command to create a userauthfile, that will be holds user accounts.
# htpasswd -cm /etc/httpd/userauthfile rhceuser01

-c Create new file and populates it with first user and password.
-m Passwords will be encrypted in MD5 before saving
Do not use -c options for creating subsequent users, otherwise it will completely override the file. Use -c option only first time for first user, from second users do not use -c option.
Restart the web server
Try again to access same sites from client, this time it will ask for user name and password

If you cancel or use wrong user name and password, access would be denied

Use correct user name and password

Upon successful authentication access would be granted

Secure web server with .htaccess file
In previous exercise we have secured entire sites. However in real life you want to allow certain parts of site publicly accessible, while other by only authenticated users. For this we will use .htaccess file.
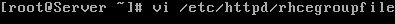
Open /etc/httpd/conf/httpd.conf file again
Change AllowOverride directive value to authconfig

In previous example we did user base authentication
Remove that and save the file

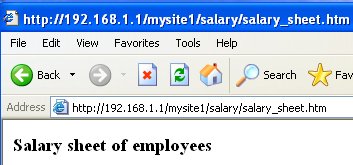
Make a directory and file under mysite1
mkdir /var/www/html/mysite1/salary
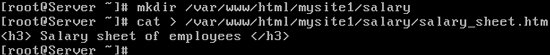
Suppose that salary folder contains the salary sheet of employees and we want to allow only hr group to access it.
Create a .htaccess file in the salary folder
#vi /var/www/html/mysite1/salary/.htaccess

Add followings and save the file
AuthType Basic AuthName “Password Restricted Area” AuthGroupFile /etc/httpd/rhcegroupfile Require group hr

Now only users from hr group, defined in /etc/httpd/rhcegroupfile can assess this.
Create few more accounts

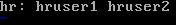
Create rhcegroupfile, this file will hold entry for groups
Add user accounts in hr group and save file
Update the SELinux context of .htaccess file

Restart the web server
Try again to access site for client, access to other parts of site are allowed except salary
To access salary folder you need to provide user name and password

Upon successful authentication access would be granted
Configure public_html folder in user home directory
httpd.conf file includes a commented directive UserDir public_html just under the default UserDir disable , when it's enabled, it allows users to browse and access the public_html directory within their home folder.
Open /etc/httpd/conf/httpd.conf file
Comment the default directive

Uncomment the UserDir public_html directive and save the file

Now anyone will have access to web pages that a user puts in his ~/public_html directory. This option can be useful if you want each user to share files over the Web. For this option you need to make users home directory executable for world. You also need to make public_html readable and executable. By default this option is disable because this requires a bit of security compromise. So unless you need to be able to share content out of a users home directory, do not enable this option. If you have to enable it in real world, take all caution in setting up this option.
Create a new normal user
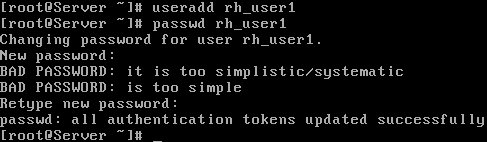
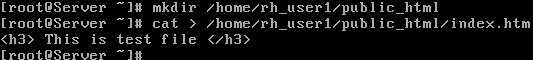
Make public_html folder under his home folder and create a test file in public_html folder
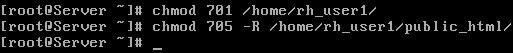
Change file permission
Enable SELinux Boolean associated with home directory
Restart the web server
Access it from client system by typing 192.168.1.1/~rh_user1/index.htm

How to create virtual hosts
Virtual host feature of Apache allows you to define multiple web sites on single IP address. For Virtual hosts configuration following options are required
| NameVirtualHost | Hostname or IP address of the virtual host |
| ServerAdmin | Email address of the webmaster |
| DocumentRoot | Location of the directory, which holds virtual host files |
| ServerName | URL of the virtual host |
| ErrorLog | Location for the error log |
| CustomLog | Location for a custom log |
Suppose that we want to host a new website example.com in virtual host.
Make new directory which will hold our new site
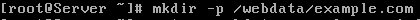
Make a sample file in new site

Update SELinux context

Open main configuration file again
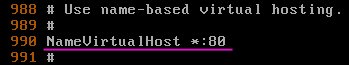
By default NameVirtualHost directive is disabled
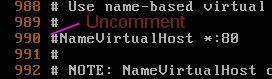
Enable it
At the end of file in virtual host section add following lines and save the file
<VirtualHost *:80> ServerAdmin webmaster@example.com DocumentRoot /webdata/example.com ServerName example.com ErrorLog logs/example.com-error_log CustomLog logs/example.com-access_log common </VirtualHost>

If you have DNS server configured update the zone files, otherwise update the hosts files . On server open the /etc/hosts file
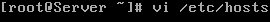
Add entry for new virtual host site and save the file

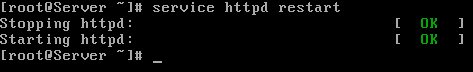
Restart the httpd service
On linuxclient system you also need to update the hosts file before testing. Open hosts file
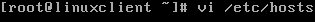
Add entry for new virtual host site and save the file

Now use elinks command to browse new site
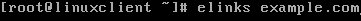
Test page confirms that we have successfully configured virtual host.

How to deploy a basic CGI application
In this section we will deploy a basic CGI application. RHCE exam objective "Deploy a basic CGI application", does not test your programming skills, so you need not to worry about programming language. You only need to know the method.
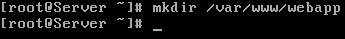
Create a directory to hold your web application:
# mkdir /var/www/webapp
Make a new sample perl file
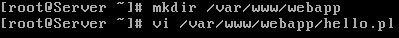
Add following in file and save the file. [This will make a sample perl script to print hello, world. Based on Apache manual]
#!/usr/bin/perl print "Content-type: text/htmlnn"; print "Hello, World!";

Update file permission and SELinux context

Open configuration file
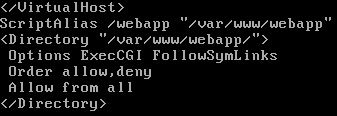
At end of file add following and save the file
ScriptAlias /webapp "/var/www/webapp" <Directory "/var/www/webapp/"> Options ExecCGI FollowSymLinks Order allow,deny Allow from all </Directory>
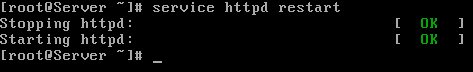
Restart the web server
On client now you can access this CGI application.

Configure secure virtual host
In this last section of tutorial we will configure a secure virtual host with self signed certificate. Make a directory to host our secure site
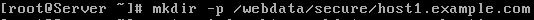
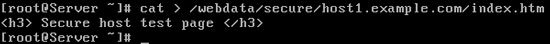
Make a sample index.htm file in it
Change file permission and Update SELinux context
Open main configuration file /etc/httpd/conf.d/ssl.conf
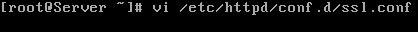
Make sure Listen Directive remain on
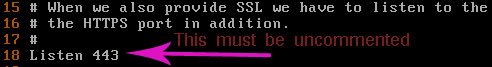
Add new Directive NameVirtualHost *:443 just above the <VirtualHost _default_:443> and replace _default_ with * in <VirtualHost _default_:443> tag.Uncomment the DocumentRoot and ServerName directives.

Change the value of directives and save the file

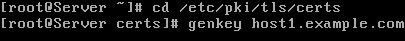
Move in certificate holder directory /etc/pki/tls/certs and use genkey command to generate new certificate and private key for secure site
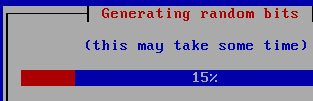
Select Next and press enter on Keypair generation window

During the exam always choose minimum available key size. Even smaller key size can take up to several minutes and in exam every minute is precious. Select 512 and move to Next tab and press enter

Wait while key generates
Select No and press enter on Generate CSR window

Keep default details and select Next and press Enter

We have sucessfully created the certificate ,now we to update the hosts file on server

Restart the httpd service
On client updated the hosts file

To test secure site open the web browser and type https://host1.example.com/index.htm in URL

You will see Untrusted connection screen Unless you purchase an actual certificate from a certificate authority (CA) such as VeriSign and Thawte. For testing we do not need third party certificate, as we have self signed certificate. Click on I Understand the Risks and Click on Add Exception

Click on confirm security exception

Test page confirms that we have successfully configured the secure virtual host

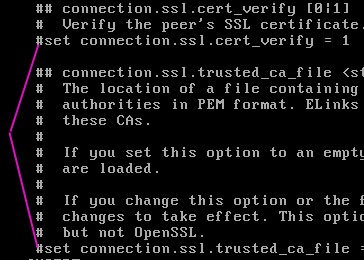
To test secure sites form elinks test based browser we need to comment two standard directives
open /etc/elinks.conf file
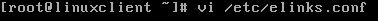
You need to comment these directives
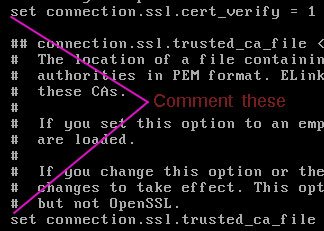
Comment them and save the file
Now you can access secure sites form elinks as well

Test page confirms our secure web hosting

When you restarts the httpd service, restart process actually stop the service from running before starting it again. This process hardly take few seconds that is ok for testing purpose but in real life where thousands of people are hitting your site, you can't afford any outage even its in seconds. In that situation you can use reload option which allows the main configuration to reread without the actually bringing service down.
#service httpd reload
One more important option which should know for real world is graceful
#service httpd graceful
This option reread the new configuration file without disconnecting any currently connected users. Only drawback of this option is that the currently active connections use the old configuration file until they terminate their connection and reconnect.
One more cool options is configtest, when used , service parses the main config file for any errors and reports back if something is found. It's your helping hand during the exam to detect any syntax errors in configuration file.
# service httpd configtest Syntax OK
If this command detect any syntax related error it return with that, otherwise it return with Syntax ok.
That's all for this article.
By ComputerNetworkingNotes Updated on 2025-12-19